
 Cyber Protect Cloud
Cyber Protect Cloud
Acronis Cyber Protect Cloud is the only solution that natively integrates cybersecurity, data protection and management to protect endpoints, systems and data. This synergy eliminates complexity, so service providers can protect customers better while keeping costs down.
Advanced AI-based behavioral detection engine for zero-day attack prevention
Full-image and file-level backup, disaster recovery, and metadata collection for security forensics
URL filtering, vulnerability assessments, and patch management for greater control

In the VB 100 certification test, Acronis detected 100% of malware and had 0% false-positives.
In the AV-Comparatives test, Acronis was one of only four solutions with zero false-positives.
In all eight performance categories for AV-TEST, Acronis demonstrated either a Very Fast or Fast performance rating.
The traditional stack of endpoint protection products lacks integration and requires much more time for management – maintaining licenses, installing updates and patches, verifying compatibility after updates, and managing multiple policies using a variety of different user interfaces.
Acronis Cyber Protect offers one agent, one management interface, and one license – removing the complexity and risks associated with non-integrated solutions.

Traditional antivirus and backup solutions are unable to protect against modern cyberthreats. Antimalware solutions that are not-integrated with backup are unable to recover data and lack the ability to detect threats in a secondary backup copy of data. Backup that is not integrated with antimalware is vulnerable to modern ransomware strains that disable and corrupt backups.
With Acronis Cyber Protect, an AI-based threat detection engine leverages backup data to improve detection rates and avoid false-positives. The integration of advanced antimalware and backup enables the automatic recovery of corrupt data. Backups are protected against attacks on the agent and backup files, ensuring the data is clean. The automatic detection, prevention, and recovery streamline your operations – reducing both the number of support calls and the time spent on each incident – making your team more efficient.
A complex, non-integrated stack of endpoint solutions requires more time to learn and support, and does not benefit from integration and automation.
Unifying multiple protection technologies into one solution not only increases its reliability, it also decreases the time needed to learn, deploy, and maintain the solution. With Acronis Cyber Protect, you get one integrated solution that delivers complete protection from today’s threats – enabling you to streamline management, cut unnecessary administrative time, and lower TCO.

No matter how great each individual solution might be, a patchwork of system and endpoint protection tools will create gaps in your clients’ defenses. Acronis Cyber Protect’s unified approach eliminates those gaps.
 AV-TEST participant and test winner 2020
AV-TEST participant and test winner 2020
 VB100 certified 2020
VB100 certified 2020
 ICSA Labs Endpoint Anti-Malware certified 2020
ICSA Labs Endpoint Anti-Malware certified 2020
 AV-Comparatives participant and test winner 2020
AV-Comparatives participant and test winner 2020
 MRG-Effitas participant and test winner 2019
MRG-Effitas participant and test winner 2019
 Anti-Malware Testing Standards Organization member 2020
Anti-Malware Testing Standards Organization member 2020
 VirusTotal member 2020
VirusTotal member 2020
 Cloud Security Alliance member 2020
Cloud Security Alliance member 2020
 Anti-Phishing Working Group member 2020
Anti-Phishing Working Group member 2020
 Microsoft Virus Initiative member 2020
Microsoft Virus Initiative member 2020
Spend more time focused on your overall security posture, rather than on managing the complexity of your protection
Avoid downtime, prevent loss of employee productivity, and spend less time on costly recoveries after successful attacks
Improve your team’s productivity and avoid the additional cost of maintaining multiple tools
Actively protect your clients from today’s advanced attacks. With Acronis Cyber Protect Cloud, you gain extended functionalities of Acronis Active Protection to protect your clients in real-time with AI-based static and behavioral heuristic antivirus, antimalware, anti-ransomware, and anti-cryptojacking technologies.
Help your clients achieve compliance and increase productivity by preventing attacks from malicious websites. With advanced URL filtering, you can control website access through a HTTP/HTTPS interceptor, black and whitelists for URLs, and payload analysis for malicious URLs.
Acronis Cyber Protection Operation Center (CPOC) continuously monitors the cybersecurity landscape and releases alert on potential threats of any kind. Receive real-time alerts on malware, vulnerabilities, natural disasters, and other global events that may affect data protection, so you can prevent them.
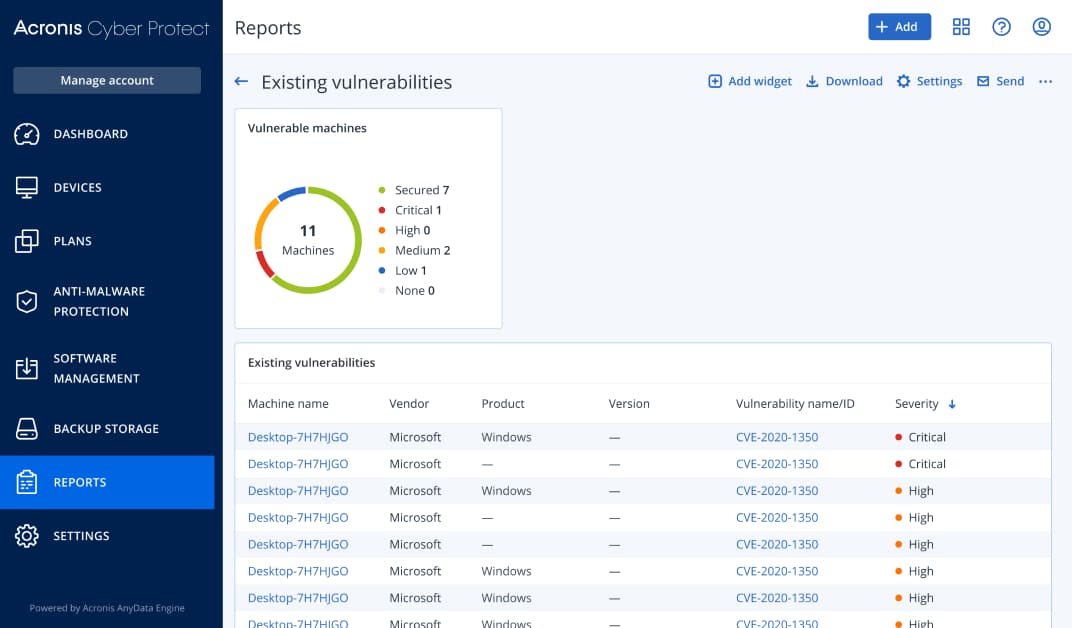
Keep your clients safer by identifying and remediating vulnerabilities in their system. With our vulnerability assessment, you can scan clients’ machines for vulnerabilities to ensure that all applications and operating systems are up-to-date and can’t be exploited by cybercriminals.
Until a patch is applied, your clients’ machines are vulnerable. With exploit prevention you can stop and prevent attacks from happening with memory protection, return-oriented programming protection, code injection protection and privilege escalation protection.
Collaboration tools like WebEx and Zoom can help an organization become more efficient, but the problem is a lot of these tools are not secure. Proactively protect these collaboration tools with vulnerability assessment, patch management, code injection prevention, and antimalware capabilities.
Maintaining compliance and running internal investigations can be an expensive process. With the Forensic Mode built-into Acronis Cyber Protect Cloud, you can simplify future analysis by collecting digital evidence – like memory dumps and process information – from disk-level backups.
Ensure that critical data is protected for compliance reporting, with the data protection map. Get detailed information about stored data and use the automatic data classification to track the protection status of important files. If files are backed up or not, IT will be alerted helping you further protect clients’ data.
The OS image or applications in the backup can have vulnerabilities, and can cause continuous reinfection if malware is still active in the network. Patching the machine and applying the latest antimalware definitions allows users to restore the OS image with the latest patches, reducing the chance of a reoccurring infection.
Prevent restoring infected files from backups with built-in malware scanning. By scanning full disk backups at a centralized location, Acronis Cyber Protect Cloud can help find malware – ensuring users restore a clean, malware-free backup.
Ensure users don’t lose the work that is in-progress by defining a list of critical apps that they are frequently using. Acronis’ agent monitors every change made in the listed applications—no matter where the user saves the file – and continuously backs it up. In case the system needs to be reimaged, you can restore the data from backup and apply the latest changes, so no data is lost.
Traditional, global whitelisting does not handle custom applications well. Acronis Cyber Protect Cloud scans backups with anti-malware technologies (AI, behavioral heuristics, etc.) to whitelist organizationally unique apps and avoid future false positives.
Simplified, at a glance reporting helps streamline your operations while giving your technicians the insight they need to successfully support your clients. Customize your dashboard’s widgets to view reports on drive health, active alerts, missing updates, and more – enabling you to quickly identify and remediate problems.
A bad system patch can render a system unusable. Before the latest patches are implemented, an automatic image backup is performed so you can easily restore and rollback to a working state if there is an issue.
Employees working from home may need access to files or apps on their work machines, and they might not have a configured VPN. Share a secure link with end users so they can remotely access their machine.
Protect your clients’ remote and office workers quickly and easily by choosing one of three preconfigured protection plans. These options help you save time while ensuring you that your clients’ workloads and environments are protected.
Enable clients to quickly and easily access files from the local site or the cloud. With the Business VPN feature, clients on DR-enabled tenants can establish a secure (L2 VPN) connection to the corporate network with their personal devices so they can access the data they need to successfully do their work.
Simplify the onboarding process by installing multiple agents at once – in the cloud and on-premises. With network-based and Active Directory-based discovery your technicians can easily remotely install and apply protection plans – helping you keep clients safe.
Instead of letting business-critical data get into the wrong hands, you can now remotely wipe compromised or missing Windows devices. Built into Acronis Cyber Protect Cloud, you can successfully prevent data from being deleted by disgruntled employees or being accessed from lost or stolen devices.
Eliminate complexity while ensuring that Windows Defender is properly configured. With Acronis protection plans, you can control Windows Defender Antivirus and Microsoft Security Essentials detection events and enforce settings across multiple machines.
Your personal safety and security are our top priority. Given the current environment, we want to enable you to help clients without needing to physically touch their machines. Voice control for Acronis Cyber Protect Cloud means you can control the console hands-free.
Save time and effort with up-to-date software and hardware inventory information. Discover all software/hardware assets installed on customer machines through automatic or on-demand scans. In addition, you can browse and filter software/hardware assets by multiple criteria, easily generate inventory reports, and auto-delete records once a machine or tenant is removed.
Purpose-built for service providers, Acronis’ cyber protection solutions – Acronis Cyber Protect Cloud and Acronis Cyber Backup Cloud – deliver easy, efficient, reliable and secure cyber protection for all data, apps and systems.
| Backup | Essentials | Standard | Advanced |
|---|---|---|---|
| Workstations, Servers (Windows, Linux, Mac) backup | |||
| Virtual machine backup | |||
| Public cloud VM agent-based backup (Azure Google, Amazon) | |||
| VMware vSphere VM agentless backup | |||
| Hyper-V VM agentless backup | |||
| VMware vSphere VM agent-based backup | |||
| Hyper-V VM agent-based backup | |||
| File-level backup | |||
| Entire machine and disk-level backup | |||
| Mobile backup (iOS, Android) | |||
| ESXi configuration backup | |||
| NAS/shares backup | |||
| Standard applications backup (Microsoft 365, G Suite, Microsoft Exchange, Microsoft SQL, Microsoft SharePoint) | |||
| Advanced applications backup (Microsoft SQL and Microsoft Exchange clusters, Oracle DB, SAP HANA) | |||
| Active Directory domain controller backup/restore | |||
| Backup to local storage | |||
| Backup to cloud storage | |||
| Cloud storage included into device license (amount depends on device type and edition) | |||
| Backup Options | Essentials | Standard | Advanced |
| Archive encryption | |||
| Incremental/differential backups | |||
| Multi-destination backup (backup replication) | |||
| Archive compression | |||
| Backup validation (checksums) | |||
| Retention rules | |||
| Backup notarization | |||
| Cybersecurity | Essentials | Standard | Advanced |
| Acronis Active Protection | |||
| Vulnerability assessment (VA) and patch management (PM) | |||
| Antivirus and Antimalware protection, Exploit prevention, URL filtering | |||
| Forensic mode, scan backups for malware, safe recovery, corporate whitelist | |||
| Threat feed | |||
| Remote device wipe | |||
| HDD Health Essential | |||
| HDD Health Extended | |||
| #CyberFit Score (protection assessment) | |||
| Continuous data protection | |||
| Backup scan for malware | |||
| Data protection map | |||
| Management & Monitoring | Essentials | Standard | Advanced |
| Group management of devices | |||
| Centralized plans management | |||
| Dashboards and reports | |||
| Email notifications | |||
| Mass update for agents | |||
| Predefined user roles: admin and user | |||
| Provisioning and management of users through Active Directory integration | |||
| Management of multiple company branches (set quota, delegate management, etc.) | |||
| Cyber Protection Desktop | |||
| Software inventory | |||
| Hardware inventory | |||
Acronis Cyber Protect Cloud is a part of the powerful Acronis Cyber Cloud platform, enabling service providers to use one solution for delivering backup, disaster recovery, secure cloud storage, file sync and share, notarization, and e-signature services to clients. In turn, Acronis Cyber Protect Cloud provides MSPs like yours with smooth and quick deployment, and a service-rich solution portfolio that increases ARPUs.